To prevent Email Sender Address Forgery Spamming, today SPF Sender Policy Framework TXT text records have been added to Domain Name Server DNS settings for all clients of I.T.ZAP Website Design Works.
This has occurred to combat the painfully persistent and utterly despicable activities of vandal Hackers and Spammers who have been sending out email messages that falsely purport to come from your business email address, when in fact they certainly do not. The problem is now being experience worldwide, as reported in precise details here ⇒
Email sender address forging is nothing new. This spamming technique is commonly known as a “Joe Job”.
Fake emails sent out to people in your computer's address book ?
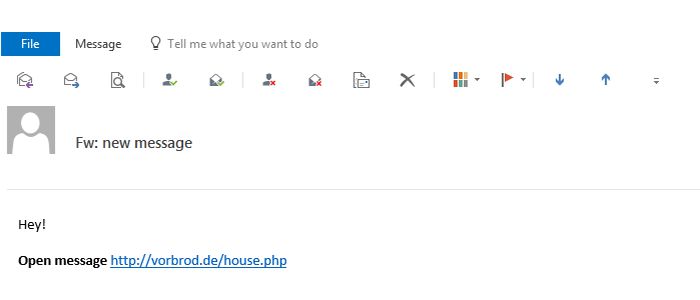
Have you received an email message that looks like this ? DO NOT click that link !
Now if you have encountered this already, take note that these fake email messages, allegedly sent by you, will most likely have been sent to people in your own email address book ! It is therefore possible that your computer has been compromised and infected by a Virus and/or Malware.
Your very first step is to run thorough scans using Anti-Virus and Malware software like :
-
Bitdefender, Norton or some other reputable anti-virus scanner, and also
-
Malwarebytes.
Clean any infections found and reboot.
What is the SPF Sender Policy Framework ?
Today, nearly all abusive email messages carry fake sender addresses. The victims whose addresses are being abused often suffer from the consequences, because their reputation gets diminished and they have to disclaim liability for the abuse, or waste their time sorting out misdirected bounce messages.
The Sender Policy Framework (SPF) is an open standard specifying a technical method to prevent sender address forgery. The owner of a domain specifies their mail sending policy, e.g. which mail server they use to send mail from their domain. This information is contained in an SPF text record in the domain's DNS zone.
How does the Sender Policy Framework work ?

-
Your SPF record will say that any email message sent is not valid, UNLESS it validates as originating from a Mail Server with your particular IP address and also your particular Website Domain Name.
-
Destination mail servers receiving an email purporting to be from your domain WILL GO and CHECK whether the message complies with your domain's stated policy. i.e. Did that email actually originate from your Mail Server IP address and your Website Domain Name ?
-
If the answer is YES, the message did originate from your IP and domain name, then the email will be validated as AUTHENTIC and delivered to the named recipent(s).
-
If the answer is NO, the email message actually originated from some unknown server with IP different to yours, then it will be intercepted as a FAKE and REJECTED. The message will not be delivered to the recipient(s).
I am confident that this will now resolve the “Joe Job” fake email problem for ITZAP clients. But if there happens to be any further repetition encountered whatsoever, then please do advise me ⇒
Update November 2016
On our new Litespeed cPanel Web Server, SPF Sender Policy Framework is a standard feature for all outgoing email from your domain.
DKIM DomainKeys Identified Mail is an additional feature. This is a means of verifying incoming email. It ensures that incoming messages are unmodified and are from the sender from whom they claim to be. This feature works to prevent incoming spam messages.
https://itzap.com.au/
https://itzap.com.au/pics/itzap-ecommerce-templates-accredited-specialist.jpg
117 Princes Highway
Lucknow
Victoria
3875
AU
+613 499 347 269
$399 to $1,500